Aton held its “Aton Security Summit 2026” in Seoul on May 13, laying out practical security response strategies for enterprises grappling with fast-moving AI adoption—an inflection point that is boosting productivity while simultaneously sharpening the sophistication of hacking, data leakage, and authentication threats.
The event, hosted at the FKI Tower Grand Ballroom in Yeouido, brought together roughly 300 attendees including chief information security officers (CISOs) from financial institutions and major corporations. The central message was that AI-driven transformation is widening the attack surface across cloud services, third-party software supply chains, and identity systems—forcing companies to rethink security as an operating model rather than a patchwork of point solutions.
In his opening remarks, Aton CEO Gil-soo Woo argued that repeated security incidents are less about a lack of tools and more about the absence of a company-wide execution framework. He urged organizations to move beyond isolated deployments of security products and instead establish unified operational principles and incident-response procedures that cut across departments. Woo also signaled Aton’s ambition to expand from its fintech security roots into a broader security provider spanning cloud and AI environments, positioning the company to serve enterprises whose risk profiles are changing alongside their infrastructure.
Park Sang-won, head of the Financial Security Institute, underscored the growing strategic role of authentication as threats diversify, including attacks that leverage AI. He framed robust authentication as the foundation of trust in financial security and emphasized the importance of financial firms building self-directed, autonomous security frameworks rather than relying solely on external mandates.
Keynote speakers warned that internal readiness is lagging behind the pace of technological change. Seung-joo Kim, a professor at Korea University’s Graduate School of Information Security, addressed the shift toward a national network security framework known as N2SF. While industry debate often focuses on government guidelines, Kim said a larger barrier is that many companies still lack basic capabilities such as data classification and risk modeling. He described a structured approach—categorizing information as confidential, sensitive, or public—as a starting point for embedding security into operations. In practical terms, this enables differentiated access controls and protection levels based on information criticality, moving beyond legacy approaches centered on physical network separation.
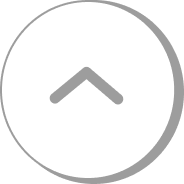
From a governance perspective, Hong-sun Kim, an adviser at Kim & Chang, argued that AI models differ fundamentally from traditional IT systems in structure and behavior, making it unrealistic to pursue a “block everything” mindset. Instead, he said boards and executive teams should treat 'cyber resilience'—the ability to restore systems quickly and normalize operations after an intrusion—as a core management metric. The emphasis reflects a broader shift in enterprise security thinking: accepting that breaches may occur while focusing on limiting blast radius, shortening downtime, and strengthening recovery workflows.
Security practitioners also highlighted how AI is changing the economics of attacks. Se-jun Park, CEO of Theori, warned that AI can dramatically lower the cost of discovering vulnerabilities that previously required extended expert analysis. He pointed to emerging real-world scenarios such as deepfake-enabled fraud conducted through real-time video conferencing, a tactic that can exploit human trust and bypass conventional verification routines.
During a dedicated session, Aton proposed an “ABCD strategy” as an immediate set of priorities for enterprises: 'zero trust' (continuous verification of users and devices), attack surface management, supply chain security, and building external cooperation frameworks. Hyun-seok Jung, head of the Aton Security Center, said the approach reflects a world where defending only the boundary between internal and external networks is no longer sufficient. Instead, companies need security controls that extend across vendors, cloud environments, and the full software delivery lifecycle—areas increasingly targeted by sophisticated adversaries.
The summit’s takeaway was clear: as AI accelerates digital operations, security is being reframed from a discretionary expense to a determinant of business continuity. Industry participants suggested this shift—already pronounced in finance due to regulatory scrutiny and trust requirements—could broaden rapidly into other sectors, prompting a wider redesign of enterprise security strategy in the year ahead.
🔎 Market Interpretation
- AI adoption is expanding enterprise attack surfaces: As companies operationalize AI to gain productivity, exposure increases across cloud services, identity systems, and third-party software supply chains—raising the probability and impact of breaches.
- Security is shifting from tools to an operating model: Speakers emphasized that recurring incidents stem less from missing products and more from weak cross-functional execution frameworks (principles, procedures, ownership, and rehearsed response).
- Authentication becomes a strategic control point: With AI-enabled attacks proliferating, strong authentication is positioned as the foundation of trust—especially in financial services where regulatory pressure and customer confidence are paramount.
- Policy frameworks meet capability gaps: Even as Korea’s national network security direction (N2SF) advances, many organizations lack fundamentals like data classification and risk modeling, limiting practical implementation.
- Resilience over “perfect prevention”: Governance guidance is moving toward cyber resilience as a board-level metric—accepting intrusions may occur while prioritizing containment, recovery speed, and continuity.
- Attack economics are improving for adversaries: AI can reduce time and cost to find vulnerabilities and enable new fraud vectors (e.g., real-time deepfake video calls), pressuring enterprises to upgrade verification and response playbooks.
- Vendor positioning: Aton signaled expansion from fintech security into broader cloud/AI security services, aligning product strategy with enterprise infrastructure shifts.
💡 Strategic Points
- Build a company-wide security execution framework: Define shared operational principles, incident-response runbooks, escalation paths, and measurable responsibilities across IT, security, legal, HR, procurement, and business units.
- Adopt “ABCD” priorities for immediate uplift:
- A — Zero Trust: Continuous verification of users/devices; reduce implicit trust in internal networks; enforce least privilege and strong session controls.
- B — Attack Surface Management: Maintain an inventory of internet-facing assets, cloud resources, identities, APIs, and AI endpoints; continuously scan for misconfigurations and exposed services.
- C — Supply Chain Security: Strengthen controls over vendors, SaaS, open-source dependencies, and CI/CD pipelines; require security assurances, logging, and patch SLAs; monitor third-party risk continuously.
- D — External Cooperation Frameworks: Coordinate with regulators, ISAC/industry groups, threat-intel partners, and incident-response firms; pre-negotiate data-sharing and response procedures.
- Start with data classification to make security actionable: Categorize information as confidential/sensitive/public to drive differentiated access controls, encryption requirements, retention, and monitoring—enabling protection based on business criticality.
- Modernize beyond “network separation”: Replace perimeter-only assumptions with identity-, data-, and workload-centric controls that work across hybrid cloud and vendor ecosystems.
- Elevate cyber resilience to a management KPI: Track and improve detection-to-containment time, recovery time objectives (RTO), restoration success rates, and blast-radius reduction—so leadership optimizes continuity, not just prevention.
- Harden authentication against AI-enabled fraud: Add phishing-resistant MFA, step-up verification for high-risk actions, and out-of-band checks for executive approvals; specifically train staff for deepfake/video-call social engineering.
- Close “readiness gap” with capability baselines: Establish minimum standards for asset inventory, logging/telemetry, vulnerability management, and risk modeling to keep pace with AI-driven change.
📘 Glossary
- CISO: Chief Information Security Officer; executive responsible for an organization’s security strategy and risk management.
- Attack surface: All possible entry points an attacker can target—systems, identities, APIs, cloud services, and third-party connections.
- Software supply chain: The components and processes used to build and deliver software (libraries, vendors, CI/CD, deployment tooling) that can be compromised.
- Zero Trust: A security model assuming no implicit trust; continuously verifies user/device/context and enforces least-privilege access.
- Attack Surface Management (ASM): Continuous discovery, monitoring, and risk reduction of exposed digital assets and configurations.
- Data classification: Categorizing data by sensitivity/criticality (e.g., confidential/sensitive/public) to apply appropriate controls and policies.
- Risk modeling: Structured assessment of threats, likelihood, and impact to prioritize controls and investments.
- N2SF: National network security framework referenced by speakers; a policy direction emphasizing modern security architecture beyond legacy perimeter separation.
- Cyber resilience: The ability to withstand attacks and rapidly restore normal operations—focusing on recovery, continuity, and limiting impact.
- Blast radius: The extent of damage an intrusion can cause; a smaller blast radius means better segmentation and containment.
- Deepfake fraud: AI-generated or AI-altered audio/video used to impersonate individuals and manipulate trust, often to authorize payments or access.
- CI/CD: Continuous Integration/Continuous Delivery; automated pipelines that build, test, and deploy software—high-value targets for supply chain attacks.


























Comment 0