As debate grows over whether quantum computing could one day crack today’s cryptography, analysts are drawing sharper distinctions between how Bitcoin (BTC) and Ethereum (ETH) might fare under a credible quantum threat—arguing that structural design choices could make Ethereum faster to expose, even if the danger remains largely theoretical for now.
The core issue is what security researchers call CRQC—cryptographically relevant quantum computers capable of breaking widely used public-key schemes. While most experts still place CRQC years away, the discussion is increasingly shifting from “can it happen” to “where would it hit first,” as investors and protocol developers weigh long-term resiliency alongside present-day cyber risks.
Public key exposure: why Ethereum may be visible sooner
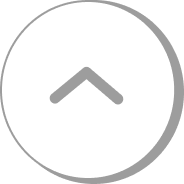
One of the biggest differences between the two networks lies in how and when public keys become visible. Bitcoin commonly relies on address formats such as ‘P2PKH’, where users publish a hash of the public key rather than the public key itself. In practice, that means a Bitcoin public key often stays hidden until coins are actually spent—making it harder for an attacker to pre-select targets at scale before on-chain activity occurs.
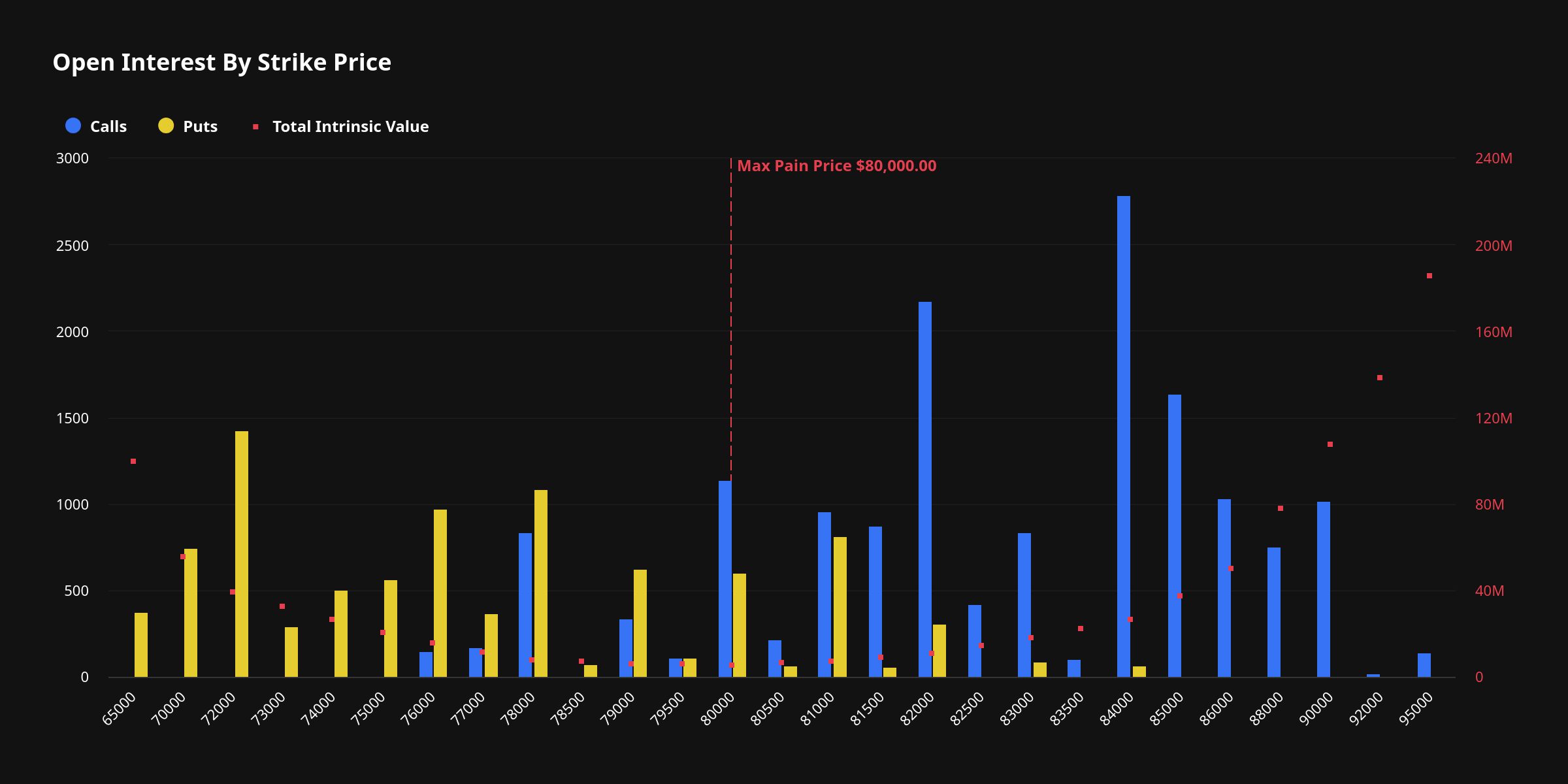
Ethereum, by contrast, uses an account-based model. Once an account has broadcast a transaction, its public key can be inferred from the signature and is widely treated as effectively exposed thereafter. If quantum decryption becomes feasible, that persistent exposure could give attackers a longer runway to catalogue and prioritize targets, analysts argue.
Broader cryptographic footprint: ECDSA plus BLS
Differences also emerge in the signature systems each ecosystem depends on. Bitcoin primarily uses ‘ECDSA’ for transaction signatures. Ethereum uses ECDSA for user accounts as well, but also relies on ‘BLS’ signatures for core proof-of-stake functions tied to validators and staking operations.
Both ECDSA and BLS are considered vulnerable in principle to Shor’s algorithm on sufficiently powerful quantum hardware. However, observers note that BLS is linked to large swaths of Ethereum’s infrastructure: validator keys, staking-related permissions, and critical operational roles. That connection leads some researchers to characterize Ethereum’s potential ‘attack surface’ as broader because multiple cryptographic systems would need to be migrated and secured in parallel.
Different failure modes: “real-time” vs “long-horizon” attack scenarios
If quantum attacks became operational, the two networks could face different threat profiles. In Bitcoin, the risk is often described as ‘timing-based’: when a transaction is broadcast to the network and sits in the mempool, the public key becomes visible, creating a theoretical window for an attacker to reconstruct the private key quickly enough to redirect funds before confirmation.
Ethereum is framed as more susceptible to a ‘long-horizon’ scenario. Because many accounts have had their public keys exposed for extended periods after transacting, an attacker could potentially harvest data over time and attempt decryption later—an approach sometimes described as “long grind.” In this view, Bitcoin’s main challenge would be preventing fast, opportunistic interception, while Ethereum’s would be mitigating accumulated exposure across widely used accounts.
Migration dynamics: Ethereum seen as more flexible, Bitcoin more conservative
Despite the concerns, some analysts argue Ethereum may have an advantage in adapting—specifically in how quickly it could implement post-quantum cryptography, or ‘PQC’. Bitcoin’s UTXO design and culture of minimal, conservative changes mean that altering signature primitives would likely require lengthy coordination, broad consensus, and careful rollout to avoid fragmenting the network.
Ethereum’s multi-layer architecture—spanning the EVM, validator mechanisms, and newer tooling such as ‘account abstraction’—is viewed as offering more pathways to staged upgrades. That flexibility could allow Ethereum to transition signature schemes incrementally, potentially speeding adoption if the perceived threat rises.
Near-term reality: traditional hacks still dominate
Even proponents of quantum preparedness emphasize that today’s dominant risks remain conventional: phishing, compromised key management, smart contract vulnerabilities, and operational failures. In that sense, the quantum debate is best treated as a medium- to long-term planning challenge rather than an imminent market catalyst.
Still, the strategic takeaway is converging. If quantum computing reaches cryptographically relevant scale, both Bitcoin and Ethereum would ultimately need a PQC transition. The race will likely hinge less on which chain is “safe today” and more on ‘migration speed’—how quickly each ecosystem can coordinate upgrades, move users to new address formats or signature systems, and minimize disruption without undermining trust in the underlying networks.
🔎 Market Interpretation
- Quantum risk framing is shifting: The conversation is moving from whether CRQC is possible to which major network would feel impact first, influencing long-term risk premiums rather than near-term price catalysts.
- Ethereum perceived as earlier-exposed: Because Ethereum account public keys can be inferred after a transaction and remain effectively exposed, markets may treat ETH as having higher “quantum visibility” than BTC under a credible timeline.
- Bitcoin seen as more “target-selection resistant”: Common Bitcoin flows hide public keys until spending, reducing pre-selection at scale and making the primary risk more timing/window-based during mempool exposure.
- Infrastructure complexity matters: Ethereum’s reliance on both ECDSA (users) and BLS (validators) broadens the cryptographic footprint that would need coordinated migration, which can translate into higher perceived execution risk.
- Key market determinant becomes upgrade velocity: If CRQC nears reality, relative resilience will likely be judged less by current design and more by the ecosystem’s ability to coordinate and complete a post-quantum transition without destabilizing trust.
💡 Strategic Points
- Monitor “public key exposure” hotspots: On Ethereum, long-lived/high-value accounts that have previously transacted may be viewed as structurally more exposed. On Bitcoin, attention centers on transaction broadcasting/confirmation latency.
- Different attack scenarios to model:
- Bitcoin: “Real-time” interception risk—attacker targets the mempool window after a spend reveals a public key.
- Ethereum: “Long-horizon” harvesting—collect exposed keys over time and attempt decryption later (“long grind”).
- Migration planning is the core hedge: Both networks ultimately require PQC if CRQC materializes; preparedness is about tooling, standards, and coordinated user migration (new address formats/signature schemes).
- Ethereum may upgrade faster in theory: Multi-layer architecture (EVM, validator system, account abstraction) could enable staged PQC rollout—though wider cryptographic dependencies (including BLS) raise parallel-migration complexity.
- Bitcoin migration may be slower but narrower: Conservative governance and UTXO-based changes typically require long consensus cycles, but the primary signature surface is more concentrated (largely ECDSA for spends).
- Don’t lose sight of current dominant threats: Near-term risk remains conventional (phishing, key compromise, smart contract bugs, operational failures). Quantum preparedness is positioned as medium/long-term engineering, not immediate market shock.
📘 Glossary
- CRQC (Cryptographically Relevant Quantum Computer): A quantum computer powerful enough to break commonly used public-key cryptography at practical cost/time.
- PQC (Post-Quantum Cryptography): Cryptographic schemes designed to resist attacks from quantum computers.
- Public key exposure: When a public key is revealed on-chain or can be inferred; relevant because Shor-capable quantum systems could derive the private key from it.
- P2PKH (Pay-to-Public-Key-Hash): A common Bitcoin address/spending pattern that initially reveals only a hash of the public key; the public key is typically disclosed when funds are spent.
- UTXO model: Bitcoin’s “unspent transaction output” accounting method; users spend discrete outputs, and public keys often appear at spend time.
- Account-based model: Ethereum’s balance-and-nonce accounting; transaction signatures can allow the public key to be inferred after an account transacts.
- ECDSA: Elliptic Curve Digital Signature Algorithm used for signing transactions; vulnerable in principle to Shor’s algorithm on sufficiently capable quantum hardware.
- BLS signatures: Boneh–Lynn–Shacham signatures used heavily in Ethereum proof-of-stake (e.g., validator operations); also theoretically vulnerable to Shor’s algorithm.
- Shor’s algorithm: A quantum algorithm that can break elliptic-curve and RSA-type cryptography by efficiently solving underlying mathematical problems.
- Mempool: The queue of unconfirmed transactions broadcast to a network; a time window where certain attacks are theorized to be more feasible.
- Attack surface: The total set of components/keys/paths an attacker could target; broader surfaces generally mean more migration and monitoring complexity.
- Account abstraction: Ethereum-focused design/tooling that makes accounts more programmable, potentially enabling staged security and signature upgrades.
























Comment 0