Drift Protocol, a Solana-based derivatives decentralized exchange (DEX), has suffered a major exploit that drained an estimated $200 million to $285 million in user assets, intensifying security concerns across the Solana DeFi ecosystem and reviving questions about oracle design and admin-key risk.
The attack occurred on Wednesday UTC (early Thursday in South Korea), according to on-chain tracing and statements from the project. Market observers are calling it one of the largest DeFi hacks of 2026 so far, with estimated losses exceeding the year-to-date DeFi total cited by several industry trackers before the incident.
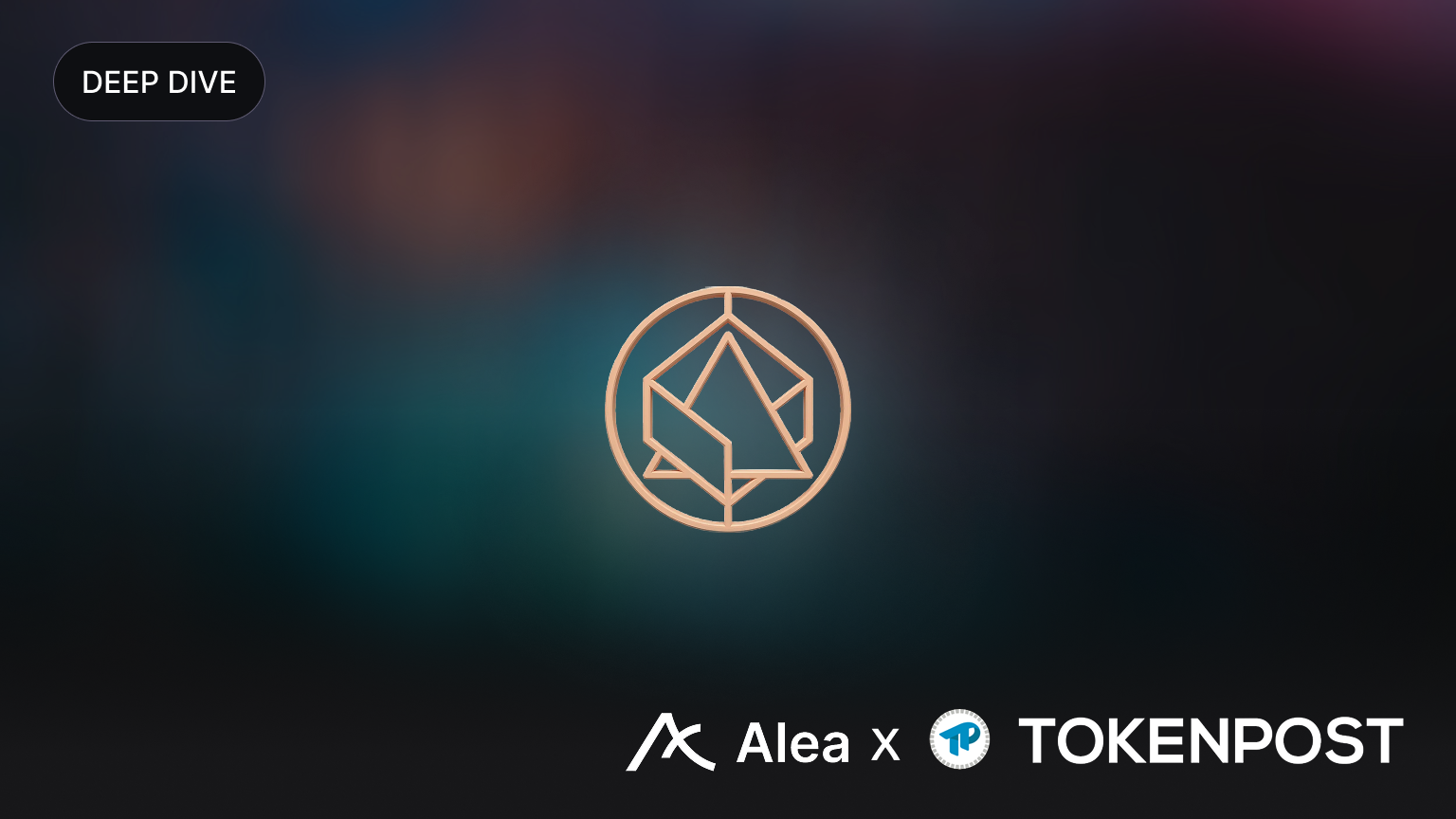
On-chain data suggests the stolen assets were broadly diversified rather than concentrated in a single token. Analysts tracking the incident reported that roughly $100 million worth of USD Coin (USDC) was among the largest components, alongside approximately $54 million in Solana (SOL), more than $30 million in bitcoin-linked assets including Wrapped Bitcoin (WBTC) and cbBTC, around $12 million in Wrapped Ether (WETH), and additional stablecoins such as Tether (USDT) and USDS, as well as a range of Solana ecosystem tokens.
While Drift is best known for perpetual futures and other derivatives products, investigators said the losses were tied primarily to ‘spot market vaults’—pooled custody contracts holding deposited collateral—rather than derivatives positions. That distinction matters: it implies a direct hit to user collateral instead of liquidations or trading-related losses contained within positions.
Initial forensic narratives point to a two-pronged technique combining ‘oracle manipulation’ with privilege abuse. The attacker allegedly introduced a fake token labeled “CarbonVote Token (CVT)” to distort oracle pricing, then leveraged what appeared to be a compromised administrator key to adjust collateral settings and withdraw limits—effectively disabling safeguards long enough to empty multiple vaults. The main drain unfolded rapidly, with dozens of transactions executed in roughly 12 minutes.
Beyond the scale of the theft, the incident has unsettled market participants because it appears to expose structural weaknesses rather than a single isolated bug. Critics of the design have highlighted the risk of accepting low-liquidity assets as collateral under an oracle framework that can be gamed, as well as governance and operational reliance on a single admin key. The apparent absence—or insufficient enforcement—of baseline controls such as ‘multisig’ approvals and ‘timelocks’ has become a focal point of scrutiny, as those mechanisms are widely viewed as standard defenses against rapid, unilateral parameter changes.
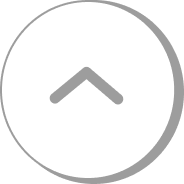
Funds have already begun moving through the broader crypto rails. Some of the proceeds were reportedly swapped into Ether (ETH) via Hyperliquid, while separate traces indicated transfers of SOL into wallets associated with Binance. That flow has fueled speculation about potential freezes if centralized exchanges cooperate, though no confirmed recovery action has been announced publicly.
The market response was swift. The DRIFT token dropped sharply in the immediate aftermath, with intraday declines reported in the roughly 25% to 37% range at its worst point. Meanwhile, Drift’s total value locked (TVL) and liquidity indicators showed signs of rapid outflows as users rushed to reduce exposure.
Drift’s team acknowledged the exploit, halted trading and withdrawals, and said it is working with Chainalysis and major exchanges to trace the stolen funds. However, the protocol has not yet published a formal compensation plan. In the absence of a confirmed roadmap, community discussions have ranged from negotiating a return of funds to potential token-based reimbursement or partial repayment through a DAO process—options that may carry significant dilution, governance, and legal implications depending on execution.
The shock has rippled beyond Drift itself. DeFi Development Corp. ($DFDV), a Nasdaq-listed company that has previously highlighted its adoption of SOL as a treasury asset, issued a statement saying it has no exposure to Drift Protocol. The quick distancing underscores how rapidly ‘contagion risk’ can become a concern for institutions and public companies engaging with crypto markets, even indirectly.
For Solana’s DeFi ecosystem, the Drift incident is shaping up as a broader stress test. It has refocused attention on the trade-offs between speed and complexity on high-throughput chains and the persistent challenges of resilient oracle design, least-privilege administration, and real-time risk controls. Whether the fallout results in stronger security standards—or a sustained pullback in user confidence—will likely depend on the transparency of the post-mortem, the effectiveness of any recovery efforts, and how quickly other protocols harden similar potential points of failure.
🔎 Market Interpretation
- Scale shock to Solana DeFi: Drift Protocol reportedly lost $200M–$285M, positioning the incident as one of the largest DeFi hacks of 2026 so far and potentially exceeding prior year-to-date totals cited by trackers before the hack.
- Collateral-side loss, not trading PnL: Damage appears concentrated in spot market vaults (custodied collateral pools), implying a direct impairment of user deposits rather than losses confined to derivatives positions or liquidation cascades.
- Immediate risk-off reaction: DRIFT token fell roughly 25%–37% intraday, while TVL/liquidity metrics showed rapid outflows—typical of confidence-driven bank-run dynamics after custody-layer exploits.
- Cross-venue fund motion raises recovery questions: Traces mention swaps into ETH via Hyperliquid and SOL transfers toward Binance-linked wallets, prompting speculation about exchange cooperation and potential freezes, though no confirmed recovery actions are public.
- Contagion sensitivity: Public-company signaling (e.g., DeFi Development Corp. stating no exposure) highlights how quickly perceived linkage can trigger reputational and balance-sheet concern across crypto-adjacent institutions.
💡 Strategic Points
- Oracle + admin-key is a compounding failure mode: The alleged combination of oracle manipulation (via a low-liquidity/introduced asset) and privilege abuse (admin key changing collateral/limits) shows how vulnerabilities stack: pricing distortion becomes catastrophic when privileged parameters can be altered without friction.
- Collateral listings need adversarial hardness tests: Accepting new/illiquid collateral should require conservative haircuts, circuit breakers, liquidity checks, and oracle robustness reviews—especially on high-throughput chains where attacks can complete in minutes.
- Enforce operational controls as protocol invariants: The scrutiny around missing/weak multisig and timelocks reinforces that “governance tooling” must be mandatory for sensitive actions (collateral parameters, withdrawal caps, oracle sources), not optional policy.
- Time-to-drain is a design metric: Dozens of transactions in ~12 minutes suggests the need for real-time risk controls: per-epoch withdrawal throttles, anomaly detection, vault-level pause switches, and permissioned emergency response with transparent audit trails.
- User playbook (risk management): Users should monitor (1) collateral composition and oracle sources, (2) admin-key architecture (multisig threshold, timelock duration), (3) vault withdrawal limits and pause policies, and (4) whether deposits are segregated vs pooled.
- Recovery paths have trade-offs: Negotiated returns, DAO-approved reimbursements, or token-based compensation can introduce dilution, governance disputes, and legal complexity; credibility hinges on a prompt post-mortem, clear claims process, and independently verifiable accounting.
📘 Glossary
- DEX (Decentralized Exchange): A trading venue operating via smart contracts rather than a centralized operator.
- Derivatives / Perpetual futures (Perps): Leveraged contracts that track an underlying price without an expiry date, typically using funding payments to anchor price.
- Spot market vault: A pooled smart-contract custody component where users deposit collateral; if compromised, losses can directly impact deposits.
- Oracle: Infrastructure that supplies external price data to smart contracts; manipulation can misprice collateral and risk limits.
- Oracle manipulation: Exploiting low liquidity, thin markets, or flawed data sources to push reported prices away from fair value.
- Admin key / Privileged access: A key (or role) capable of changing sensitive protocol parameters; if compromised, safeguards can be bypassed.
- Multisig: A wallet/security scheme requiring multiple independent approvals (e.g., 3-of-5) to execute critical actions.
- Timelock: A delay mechanism that queues parameter changes before execution, enabling community review and emergency intervention.
- TVL (Total Value Locked): Total assets deposited in a protocol; sharp drops often indicate withdrawals and confidence loss.
- Stablecoin: A token designed to maintain a stable value (commonly pegged to USD), e.g., USDC, USDT.
- Wrapped assets (WBTC, WETH): Tokenized representations of assets (BTC/ETH) used on other chains, enabling DeFi usage.
- Collateral parameters: Settings such as collateral factor/haircut, borrow limits, and withdrawal caps that define risk exposure.
- Contagion risk: The chance that one protocol’s failure triggers broader market fear, liquidity withdrawal, or institutional de-risking.

























Comment 0