Bitcoin (BTC) is once again confronting a thorny question that blends cybersecurity with ideology: if future quantum computers can crack today’s cryptography, should the network proactively ‘freeze’ an estimated 4 million BTC believed to be stranded in long-dormant wallets—or accept that those coins may eventually be stolen and sold by whoever can access them?
The debate resurfaced over the weekend after fresh discussion around “Q-Day,” the hypothetical point at which quantum systems become powerful enough to break the cryptographic assumptions that protect Bitcoin private keys. While most researchers still describe such a threat as distant, diverging forecasts have reintroduced a persistent source of medium- to long-term uncertainty for holders and infrastructure providers alike.
At the center of the dispute is a large pool of coins widely thought to be unspendable because their owners lost keys, abandoned early wallets, or died without passing on access. Those coins do not threaten the market under normal conditions because they remain inert. In a post-quantum world, however, they could become a high-value target: if an attacker could derive private keys from public information, dormant balances might be swept—potentially turning ‘dead’ supply into sudden sell pressure.
Analyst Willy Woo has warned that an abrupt reintroduction of such coins could shock market structure, amplifying downside volatility if large amounts hit exchanges in a short window. In that framing, a protocol-level intervention—such as disabling spending from legacy address types or freezing certain outputs—would be a defensive step to protect users and preserve confidence.
Adam Back, a cryptographer who contributed to Bitcoin’s early development and is now CEO of Blockstream, has pushed back hard on the idea. In a post on X dated Sunday ET, Back argued that if quantum capability ever reaches the point of practical theft, “you’ll be rugged anyway,” insisting that markets—not developers—would ultimately determine how the ecosystem responds. He also suggested that without broad consensus, no code change of this magnitude would even ship.
More fundamentally, Back warned that giving developers or any coordinating group the ability to decide which coins remain valid risks undermining Bitcoin’s neutrality. In his view, selectively invalidating or freezing coins could become its own kind of ‘rugpull’—not by hackers, but by governance pressure—damaging the system’s credibility as a permissionless monetary network. He further emphasized that wallet security and key management are individual responsibilities, not obligations the protocol can or should assume.
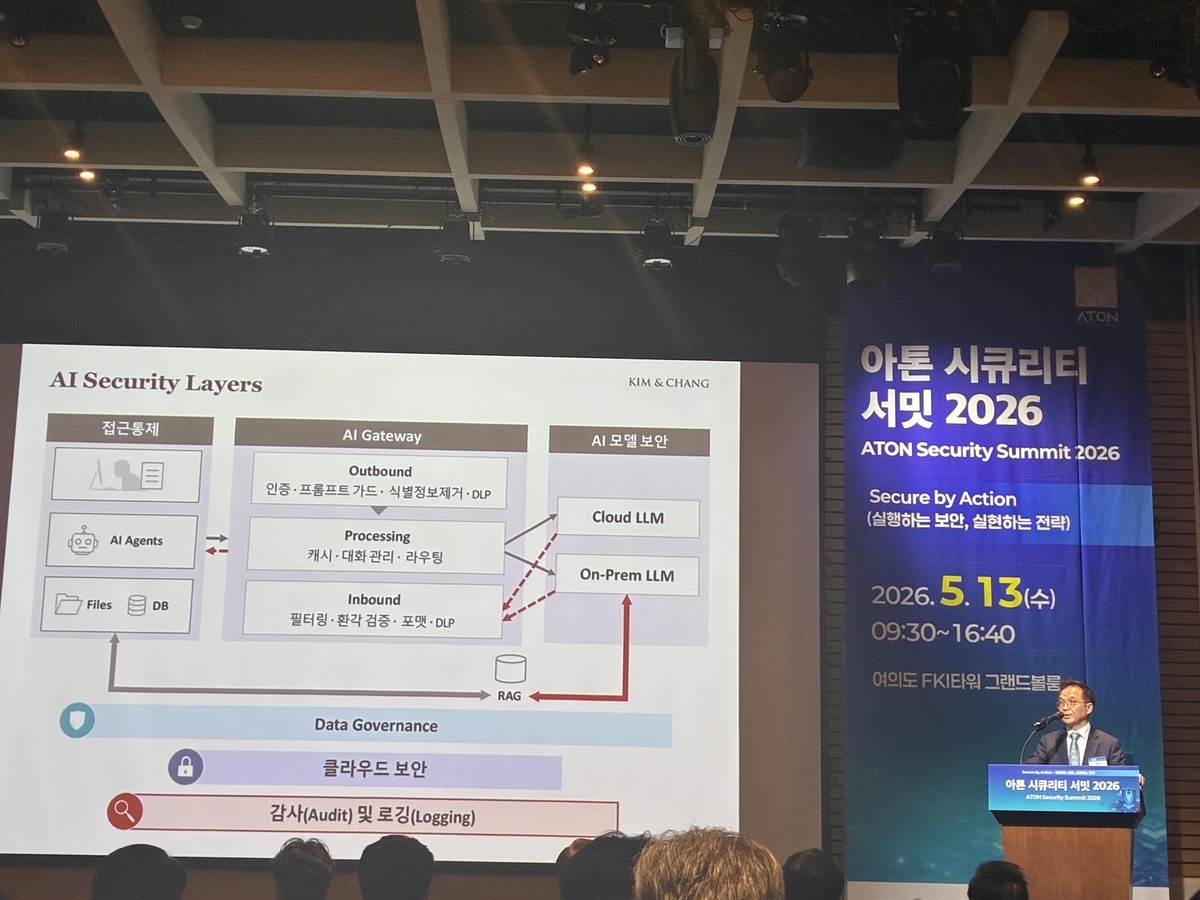
Even as the philosophical divide sharpens, technical work intended to reduce quantum risk is moving forward in parallel. Developers and researchers have discussed potential migrations toward ‘post-quantum cryptography’ (PQC), including draft proposals such as BIP-360 and other upgrade paths that would allow safer address formats and signature schemes. Industry observers note that a complete transition could take years, both because of engineering complexity and because widespread adoption would require coordination across wallets, exchanges, custodians, and hardware providers.
Global standards bodies have already approved several PQC algorithms for broader use, strengthening the argument that Bitcoin could adapt ahead of any credible quantum threat—if the community agrees on trade-offs. Yet every mitigation idea reopens a familiar fault line: whether it is acceptable to change protocol rules to protect users from an external technological shift, or whether Bitcoin must preserve ‘immutability’ and decentralization principles even if that means some losses are inevitable.
For now, the quantum threat remains theoretical in the context of Bitcoin’s current security, and timelines are hotly contested. But the renewed focus on dormant supply—and the possibility of forced protocol responses—highlights how future cryptography risks could shape not only upgrade priorities, but also long-term perceptions of Bitcoin’s legitimacy as ‘hard’ money in a rapidly evolving technological landscape.
🔎 Market Interpretation
- Core risk being repriced: The market-facing issue is not “quantum breaks Bitcoin tomorrow,” but the scenario where quantum capability makes dormant/lost coins spendable, abruptly converting inert supply into active supply.
- Dormant supply overhang: Roughly ~4M BTC believed to be stranded could become a prime target in a post-quantum environment. If swept, it may create sudden sell pressure and liquidity shocks.
- Volatility transmission channel: A rapid sweep of old outputs could funnel coins onto exchanges quickly, potentially amplifying downside volatility and widening spreads as market makers re-hedge.
- Governance premium/discount: The debate adds a “governance uncertainty” layer—whether Bitcoin would coordinate a defensive change (freezes/disabled legacy spends) or refuse, affecting long-term confidence.
- Two competing confidence narratives: (1) Intervention could reassure users about security continuity; (2) intervention could undermine the neutrality/immutability thesis and introduce perceived discretionary control.
💡 Strategic Points
- Threat model clarity: The practical quantum danger centers on cases where public key material is exposed (e.g., after spending from certain address types) rather than all coins uniformly. Risk is heterogeneous across UTXOs and wallet behaviors.
- Freeze vs migrate trade-off:
- Freeze/disable legacy spends could prevent quantum theft of dormant coins but introduces a precedent of protocol-level value judgments about which coins are “valid.”
- Migrate to post-quantum signatures preserves permissionless spending but requires large-scale ecosystem coordination and long timelines.
- Consensus is the gating factor: Even if a technical fix exists, changes of this magnitude depend on broad agreement among node operators, miners, exchanges, wallets, and custodians—otherwise they likely won’t deploy.
- Market-led vs developer-led response: Adam Back’s stance emphasizes that if quantum theft is feasible, markets will react (repricing BTC/security practices), and any “selective invalidation” may be seen as a governance rugpull.
- Operational implications (near-to-mid term):
- Wallet providers may prioritize upgrade paths that reduce key exposure and support future PQC address formats.
- Exchanges/custodians may plan phased migrations, user communications, and deposit/withdrawal policy changes tied to new script/address standards.
- Upgrade pathways are emerging: Discussion includes BIP-360 and other proposals aimed at enabling safer address/signature schemes. A full transition could take years due to engineering, backward compatibility, and adoption coordination.
- Strategic investor lens: The quantum narrative is a long-dated tail risk but can influence valuations through (a) perceived upgrade agility, (b) credibility of immutability, and (c) expectations about future circulating supply shocks.
📘 Glossary
- Q-Day: A hypothetical future point when quantum computers become powerful enough to break widely used cryptography at practical scale.
- Quantum attack (in this context): Using quantum algorithms to derive a private key from public cryptographic information, enabling unauthorized spending.
- Private key: Secret data that authorizes spending of BTC from a wallet/address.
- Public key: The publicly revealed counterpart used to verify signatures; if sufficiently exposed and cryptography is broken, it could be used to infer the private key.
- Dormant / stranded BTC: Coins stuck in long-inactive wallets due to lost keys, abandoned wallets, or unavailable inheritance/access.
- UTXO (Unspent Transaction Output): Bitcoin’s “coin” representation—an unspent output that can be spent as an input in a future transaction.
- Legacy address types: Older Bitcoin script/address formats that may have different exposure characteristics and migration constraints.
- Protocol-level freeze: A rule change that prevents certain coins/outputs from being spent, regardless of who presents a valid signature under old rules.
- Post-Quantum Cryptography (PQC): Cryptographic algorithms designed to remain secure even against quantum computers.
- BIP: Bitcoin Improvement Proposal—an open design document describing standards, processes, or protocol changes for Bitcoin.
- Immutability/neutrality (Bitcoin ethos): The principle that no party should arbitrarily change ownership outcomes; rules should be general, predictable, and permissionless.
- Sell pressure: Market impact created when increased supply is sold into the market, potentially pushing prices down.



























Comment 0